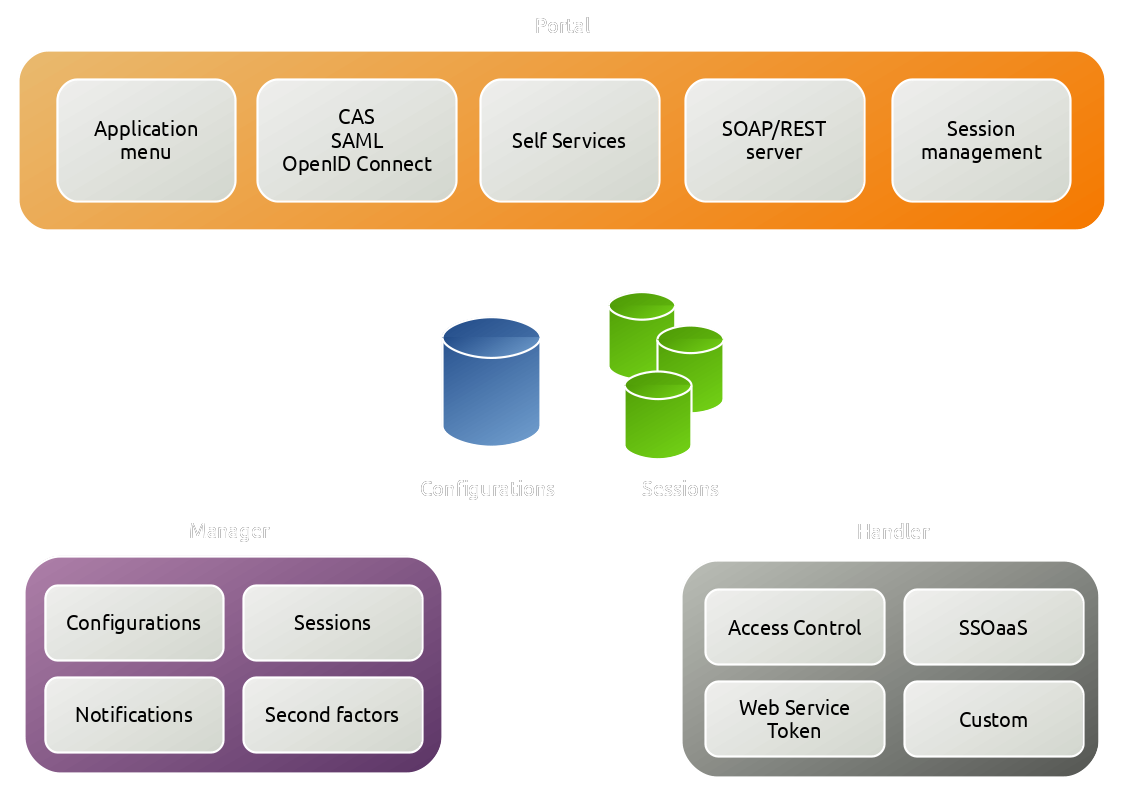
Components
LemonLDAP::NG relies on backends (files, databases, NoSQL) to store configuration and sessions. The Portal is the visible part, it displays the authentication screen and the menu, implements the standard protocols (CAS, SAML and OpenID Connect). The Manager is the administration interface. For applications working with HTTP headers for SSO, the Handler can be configured.